Data
378 articles on this topic
 Technology
Technology
How Compression Reduces File Size Without Losing Quality
Forget "finding duplicates." True lossless compression isn't magic; it's statistical genius. It exploits predictable data patterns, turning digital chaos into perfectly reconstructible order.
 Technology
Technology
Why Video Files Are So Large Compared to Images
You think video is just 30 photos a second? You're missing the true data monster: it's the complex predictions between frames, not just the frames, that balloon file sizes.
 Technology
Technology
How File Formats Affect Quality and Size
The formats you choose aren't just technical details; they're strategic decisions with measurable costs. True quality isn't perfect fidelity, it's optimal experience, often found in surprising places.
 Technology
Technology
Why Some Files Won’t Open on Your Device
Your unreadable file isn't always a technical glitch. It's often a strategic casualty in tech giants' silent war for your digital ecosystem.
 Technology
Technology
How Network Congestion Slows Internet Speed
Forget simply blaming your ISP. Internet congestion often stems from hidden global chokepoints and collective digital surges far beyond your control. It's a systemic traffic jam, not just a local one.
 Technology
Technology
Why Some WiFi Networks Require Login Pages
Your "free" Wi-Fi login isn't just about access; it's a sophisticated data contract. You're often paying with your personal information, not just your patience.
 Technology
Technology
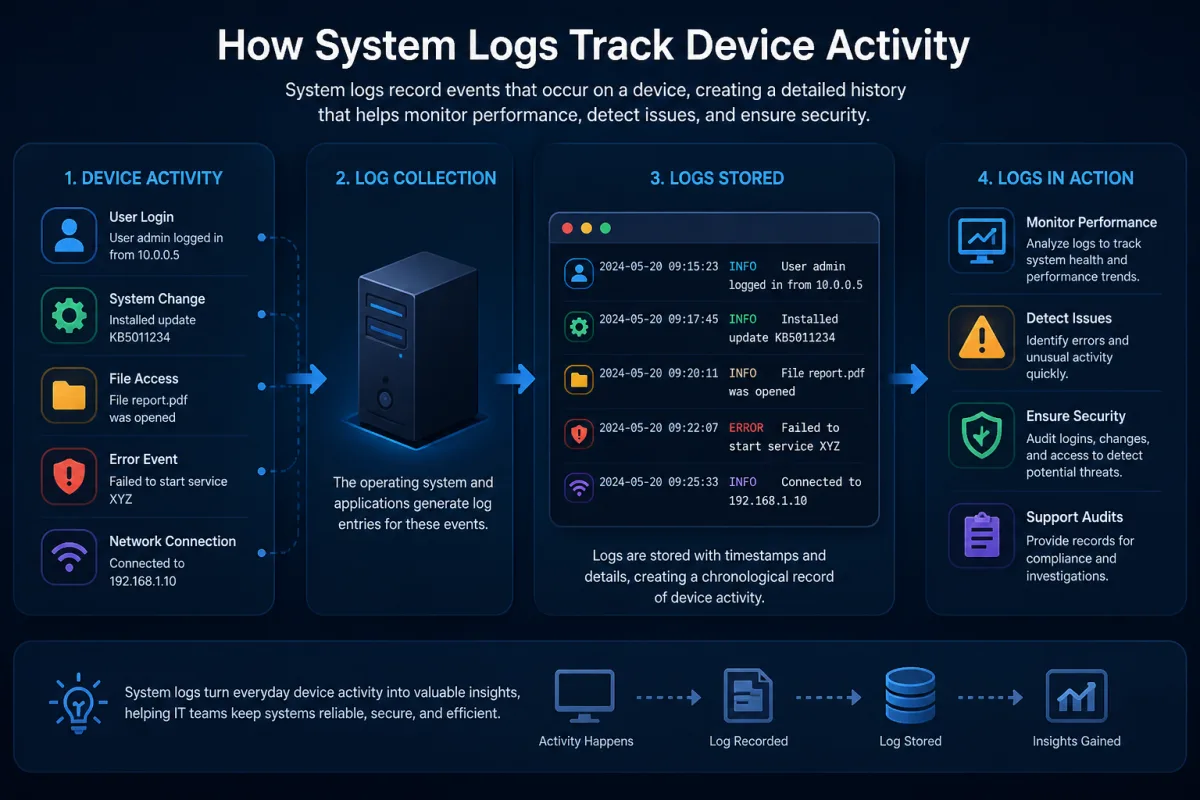
How System Logs Track Device Activity
Logs aren't just history books; they're crystal balls. Discover how these digital breadcrumbs proactively shape your device's future, often without you knowing.
How File Systems Organize Data on Your Device
Your files aren't what they seem. File systems are master illusionists, meticulously scattering and reassembling data, making invisible trade-offs that impact your device's speed and lifespan.
How Email Encryption Works in Simple Terms
Email encryption promises privacy, but it's often a digital mirage. Most "encrypted" emails aren't truly end-to-end secure, and your privacy depends on far more than you think.
Why Email Verification Is Required Everywhere
You think email verification is about spam? Think bigger. It's a critical, often legally mandated, layer preventing systemic digital fraud and preserving the internet's trust infrastructure.
How Temporary Email Services Function
Temporary email services promise privacy, but they're a dark playground for threat actors. 'Temporary' often becomes untraceable exploitation, not just a spam shield.
How Email Tracking Pixels Work
Email tracking isn't just about opens; it's an invisible surveillance network harvesting your data. Uncover the hidden tech building your digital profile.