#
It Operations
2 articles on this topic
Implementing Two-Factor Authentication across Enterprise
Enterprise 2FA isn't just a technical fix; it's a battle against human nature and hidden costs. Most implementations fail not in code, but in culture and complexity.
21 min read
 Technology
Technology
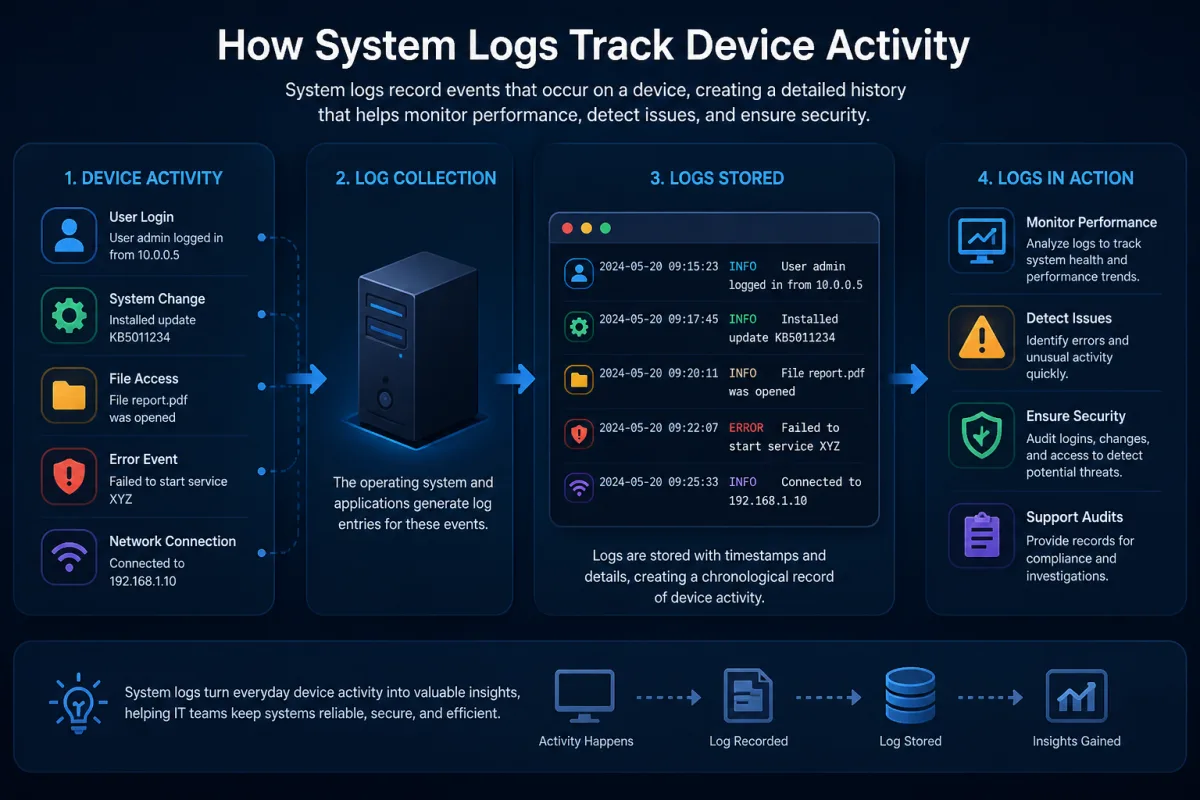
How System Logs Track Device Activity
Logs aren't just history books; they're crystal balls. Discover how these digital breadcrumbs proactively shape your device's future, often without you knowing.
16 min read